How to Install FTP server (vsftpd) on Ubuntu 18.04 / 18.10 / 19.04 / 19.10
How to Install FTP server (vsftpd) on Ubuntu 18.04 / 18.10 / 19.04 / 19.10

vsftpd (Very Secure File Transfer Protocol Daemon) is a popular FTP server for Ubuntu. In this guide we will install and configure vsftpd on Ubuntu 18.04 / 18.10 / 19.04 / 19.10. We will also set up an FTP user and optionally configure SFTP for secure file transfers.
Before you begin…
It’s surprising how many web developers are still unaware of SFTP and the advantages over FTP/FTPS. SFTP comes with Linux Server preinstalled and works just like normal FTP, but is more secure and less hassle to set up. If your FTP client supports SFTP, you should use it!
1. Install vsftpd
Let’s begin by updating the package lists and installing vsftpd on Ubuntu 18.04 / 18.10 / 19.04 / 19.10.
Below we have two commands separated by &&. The first command will update the package lists to ensure you get the latest version and dependencies for vsftpd. The second command will then download and install vsftpd. Press y and ENTER when asked to continue.
sudo apt update && sudo apt install vsftpd
Once installed, check the status of vsftpd
sudo service vsftpd status
● vsftpd.service - vsftpd FTP server
Loaded: loaded (/lib/systemd/system/vsftpd.service; enabled; vendor preset: enabled
Active: active (running) since Tue 2018-04-17 15:23:22 UTC; 10s ago
Main PID: 31602 (vsftpd)
CGroup: /system.slice/vsftpd.service
└─31602 /usr/sbin/vsftpd /etc/vsftpd.conf
Apr 17 15:23:22 myserver systemd[1]: Starting vsftpd FTP server...
Apr 17 15:23:22 myserver systemd[1]: Started vsftpd FTP server.
Above we can see our FTP server is now up and running.
2. Configure Firewall
If you haven’t already done so, it is recommended that you enable the ufw firewall for Ubuntu 18.04 / 18.10 / 19.04 / 19.10. Before enabling ufw firewall, make sure you add a rule for SSH, otherwise you may get locked out of your server if you’re connected remotely. If you don’t want to set up a firewall, skip to Step 3.
sudo ufw allow OpenSSH
Let’s open ports 20 and 21 for FTP, and ports 40000-50000 for passive FTP. We’ll also open port 990 for TLS, which we will set up later.
sudo ufw allow 20/tcp
sudo ufw allow 21/tcp
sudo ufw allow 40000:50000/tcp
sudo ufw allow 990/tcp
Now, enable the firewall if it isn’t already. Press y and ENTER if warned about disrupting the SSH connection.
sudo ufw enable
To check the status of the firewall, run:
sudo ufw status
If the firewall is running, you should see Status: active and the firewall rules we just added.
Status: active
To Action From
-- ------ ----
OpenSSH ALLOW Anywhere
Apache Full ALLOW Anywhere
3306 ALLOW Anywhere
20/tcp ALLOW Anywhere
21/tcp ALLOW Anywhere
40000:50000/tcp ALLOW Anywhere
990/tcp ALLOW Anywhere
OpenSSH (v6) ALLOW Anywhere (v6)
Apache Full (v6) ALLOW Anywhere (v6)
3306 (v6) ALLOW Anywhere (v6)
20/tcp (v6) ALLOW Anywhere (v6)
21/tcp (v6) ALLOW Anywhere (v6)
40000:50000/tcp (v6) ALLOW Anywhere (v6)
990/tcp (v6) ALLOW Anywhere (v6)
3. Create FTP User
We will now create a new user that we will use to log into FTP. In this example, we will create a new user called ftpuser.
sudo adduser ftpuser
Generate a strong password and keep it safe.
You may also be asked to enter some contact information. You can just press ENTER to each of these.
If you only want ftpuser to log in via FTP, you should disable their SSH access by blacklisting their username in the SSH config file. Otherwise, skip to Step 4.
Open the SSH config in nano.
sudo nano /etc/ssh/sshd_config
Add the following to the bottom of the file replacing ftpuser with the user you want to deny SSH and SFTP access. You can add multiple users here separated by a single space. (To paste in nano, press the right mouse button).
/etc/ssh/sshd_config
DenyUsers ftpuser
To save file and exit, press CTRL + X, press Y and then press ENTER.
Restart the SSH service.
sudo service sshd restart
4. Directory Permissions
You now need to decide where this new FTP user is allowed to view and upload files.
vsftpd uses chroot jails to restrict users to their home directories and requires that the home directory is not writable. For that reason, we have to set up some directories and permissions.
If you plan on using this FTP user account to upload files to a web server, continue to Step 4.1. If you just want to upload to a home folder, skip to Step 4.2.
4.1. Upload to a Web Server
In many cases, you want to be able to upload files to the document root on the web server.
If you followed a previous guide here for setting up multiple domains, your document root may be located in somewhere like /var/www/test1.com/public_html – in that case, you would need to set the home folder for ftpuser to the folder above the document root: /var/www/test1.com (substituting test1.com for your own domain).
If you are not using multiple domains, we will assume you are using the default document root /var/www/html for both Apache and Nginx in Ubuntu 18.04 / 18.10 / 19.04 / 19.10. In this scenario, we have to make /var/www/ the home directory for our user ftpuser.
Let’s set the folder above the document root as the home directory for ftpuser.
sudo usermod -d /var/www ftpuser
Now set ownership of the document root directory to ftpuser. (The default is /var/www/html, though it may be /var/www/test1.com/public_html on your server.)
This will allow our FTP user to write and alter files in the document root directory.
sudo chown ftpuser:ftpuser /var/www/html
Now skip to Step 5 to configure vsftpd.
4.2 Upload to a Home Folder
If instead you want this user to upload files to the home directory, create a new directory called ftp in the user’s home directory and another within it called files. In this example below our user is called ftpuser.
sudo mkdir /home/ftpuser/ftp
Set the ownership of the ftp directory to no nobody:nogroup.
sudo chown nobody:nogroup /home/ftpuser/ftp
Set permissions for the ftp directory using chmod so that it is not writable by anyone, otherwise vsftpd will not allow you to log in. a-w means a = all/everyone - = remove w = write permission, so, remove write permissions for everyone.
sudo chmod a-w /home/ftpuser/ftp
Next we will create a new directory within /ftp where the user can view and upload files.
sudo mkdir /home/ftpuser/ftp/files
Assign ownership of this directory to our new FTP user otherwise they will not be able to write to it.
sudo chown ftpuser:ftpuser /home/ftpuser/ftp/files
5. Configure vsftpd
There are a few changes we have to make to the vsftpd configuration file before you can start using FTP on Ubuntu 18.04 / 18.10 / 19.04 / 19.10.
Before editing the config file, create a backup.
sudo cp /etc/vsftpd.conf /etc/vsftpd.conf.bak
Now, open the config file in nano editor.
sudo nano /etc/vsftpd.conf
This is quite a large file but it’s mostly filled with comments to help you along.
You need to go down the file and make sure that the settings match those below. Note: you can search in nano using CTRL + W
Look for #write_enable=YES and uncomment it by removing the # sign. This will allow FTP users to write files to the server.
etc/vsftpd.conf
write_enable=YES
Look for #chroot_local_user=YES and uncomment it by removing the # sign. This will prevent FTP users from browsing outside their own directory.
etc/vsftpd.conf
chroot_local_user=YES
Look for #local_umask=022 and uncomment it by removing the # sign. This will give uploaded files and folders the correct permissions.
etc/vsftpd.conf
local_umask=022
We now need to add some directives that don’t exist in the file.
Since Linux doesn’t show files beginning with a dot, files like .htaccess will not be visible in FTP. This may be a problem if you intend to use Apache and want to work with .htaccess.
To force vsftpd to show file names that begin with a dot, paste the following to the bottom of the file. (To paste in nano, press the right mouse button)
etc/vsftpd.conf
force_dot_files=YES
Lastly, let’s add some port ranges for passive FTP to make sure enough connections are available. Paste the following to the bottom of the file. (To paste in nano, press the right mouse button)
etc/vsftpd.conf
pasv_min_port=40000
pasv_max_port=50000
If you followed Step 4.2 previously and only want this user to upload files to the home folder, we must tell vsftpd that the local_root is the /ftp folder we created earlier.
Don’t add these two lines if you want the user to upload to the web document root!
etc/vsftpd.conf
user_sub_token=$USER
local_root=/home/$USER/ftp
We are done with vsftpd.conf for the moment but will return in later steps to set up security and SSL.
To save file and exit, press CTRL + X, press Y and then press ENTER.
Restart vsftpd.
sudo systemctl restart vsftpd
6. Test FTP
We can now test vsftpd to see if we can log in as the user we created earlier. We recommend FileZilla, which works on Windows, Mac and Linux.
Enter your server’s IP, your FTP username and password you created earlier, and click Quickconnect.
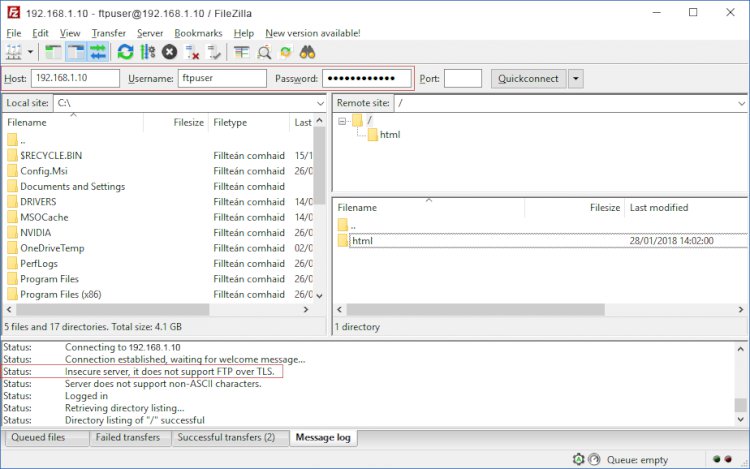
Above we can see we have connected successfully and the web root directory html is displayed, though this may be different on your server.
Try uploading, creating and editing folders and files within the web root directory to ensure permissions are working correctly.
You will notice we have a warning in FileZilla “Status: Insecure server, it does not support FTP over TLS.” It is highly recommended that you now configure TLS so that login credentials and traffic are encrypted over the FTP connection.
If you are having problems logging in to the FTP server, try checking the vsftpd log. To view the last 200 entries using tail:
sudo tail /var/log/vsftpd.log -n 200
7. Secure FTP with TLS (optional)
It’s important to keep a few things in mind when using FTP – it is not encrypted by default meaning your credentials and files that you send are vulnerable to interception. To address this you should connect to vsftpd using FTPS (FTP over SSL/TLS).
Let’s begin by creating a new certificate with the openssl tool.
sudo openssl req -x509 -nodes -days 365 -newkey rsa:2048 -keyout /etc/ssl/private/vsftpd.pem -out /etc/ssl/private/vsftpd.pem
You will be asked to enter some details like country, etc. You don’t have to fill these in. You can just press ENTER for defaults.
Now that your private key has been created, there are a few changes we have to make to the vsftpd configuration file.
Open the config file in nano editor.
sudo nano /etc/vsftpd.conf
Find the following line: (Note: you can search in nano using CTRL + W)
etc/vsftpd.conf
ssl_enable=NO
Change it to:
etc/vsftpd.conf
ssl_enable=YES
Paste in the following beneath it.
etc/vsftpd.conf
rsa_cert_file=/etc/ssl/private/vsftpd.pem
rsa_private_key_file=/etc/ssl/private/vsftpd.pem
allow_anon_ssl=NO
force_local_data_ssl=YES
force_local_logins_ssl=YES
ssl_tlsv1=YES
ssl_sslv2=NO
ssl_sslv3=NO
require_ssl_reuse=NO
ssl_ciphers=HIGH
pasv_min_port=40000
pasv_max_port=50000
Save file and exit (press CTRL + X, press Y and then press ENTER).
Restart vsftpd.
sudo systemctl restart vsftpd
8. Testing TLS with FileZilla
We can now test TLS. We recommend FileZilla, which works on Windows, Mac and Linux.
Enter your server’s IP, your FTP username and password you created earlier, and click Quickconnect.
You may be presented with an Unknown Certificate warning. Click Always trust this certificate in future sessions and click OK.
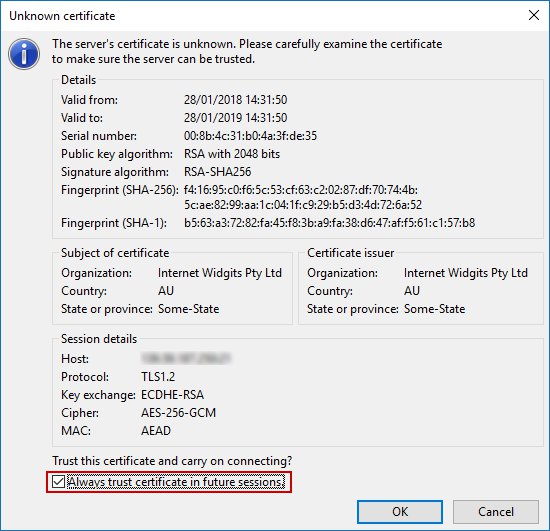
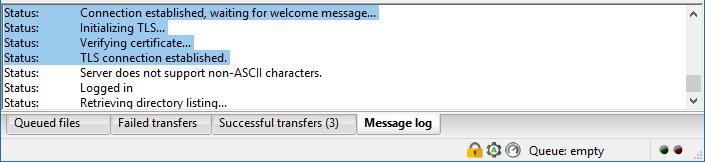
If you are connected over TLS, it will tell you in the connection log. You will also see a padlock in the bottom right corner.
Well we are done!